Microsoft is once again advising its customers to disable Windows print spooler, after a new vulnerability that allows hackers to execute malicious code on machines has emerged. While a patch fixing the flaw will be released in due course, the most effective workaround currently on the table is to stop and disable the print spooler service entirely.
This is the third print spooler vulnerability to emerge in just five weeks. While a critical flaw was originally identified and patched in June, a similar flaw – dubbed PrintNightmare – came to light shortly after and was subsequently patched (with mixed success).
The emergence of this new vulnerability is frustrating news for Microsoft and its users.
Microsoft has warned customers of the new print spooler vulnerability online, writing: “An elevation of privilege vulnerability exists when the Windows Print Spooler service improperly performs privileged file operations. An attacker who successfully exploited this vulnerability could run arbitrary code with SYSTEM privileges. An attacker could then install programs; view, change, or delete data; or create new accounts with full user rights.”
This is very important!
If you have the “Print Spooler” service enabled (which is the default), any remote authenticated user can execute code as SYSTEM on the domain controller.
Stop and Disable the service on any DC now! https://t.co/hl0NItsrBF pic.twitter.com/s4yE2VVl5I— Will Dormann (@wdormann) June 30, 2021
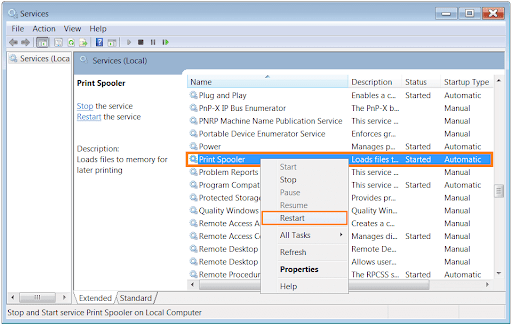
The bottom line in terms of making your computer safe is to stop and disable the print spooler service outright, if it’s running – Microsoft spells out how you can do so online. While there’ll be a patch for this vulnerability released in due course, no timeline is currently available.

