For the longest time, cybercriminals have been exploiting the macro feature in Office applications like Word and Excel to infect unsuspecting users’ PCs with malware. They typically do this by injecting malicious macro code into a legitimate Word or Excel document, then convincing users to enable macros to allegedly display the file properly. However, this only allows the malware to wreak havoc into the victim’s PC.
Microsoft is aware of this behavior by threat actors, so they eventually blocked macros in Office documents by default. However, cybercriminals are now using another app to trick users into infecting their own PCs with malware: digital note-taking app OneNote.
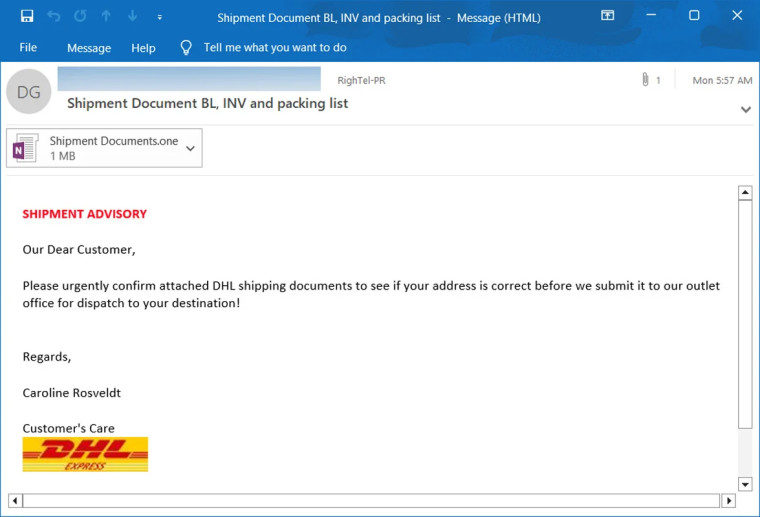
As reported by BleepingComputer, cybercriminals have been found sending phishing emails that purportedly contain DHL invoices, remittance forms, shipping notifications and documents, and mechanical drawings. Instead of using macros, which OneNote does not support, cybercriminals are exploiting OneNote’s ability to attach files within a notebook.
They do this by attaching malicious VBS files onto a OneNote notebook. When double-clicked, these files automatically download and install malware from a remote site. To conceal them and make the OneNote document look as legitimate as possible, threat actors overlay a “Double click to view file” box over them.
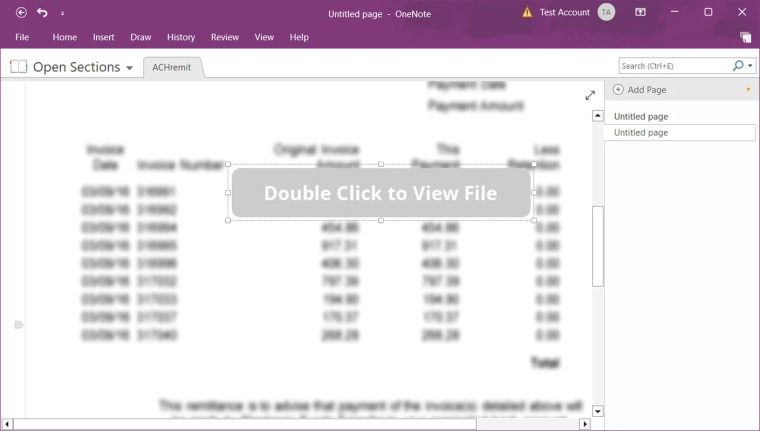
This means that clicking on the box will launch the malicious files, which will install malware onto the device. And while OneNote will warn users that opening attachments could harm the user’s computer and data, many users might just ignore the warning and click “OK” anyway.
In the emails seen by BleepingComputer, the malicious OneNote documents typically install remote access trojans that can steal sensitive information and cryptocurrency wallets. Others can even take screenshots and record video using the victim’s webcam.
To protect yourself from these attacks, do not open unsolicited emails from people you do not know. Also, make sure that your antivirus software is updated so it can properly detect malware and remove it from your system.
Source and images: BleepingComputer




